Many Chief Information Security Officers accept that simply not having enough hours in the day comes with the territory. It is a constant juggling act between meetings, their resulting action points, the smooth running of your organisation’s IT department and not forgetting the huge prioritisation of cybersecurity and regulatory compliance.
As we accelerate towards a digital infrastructure dominated by IaaS, DaaS and SaaS applications, CISOs face an increasingly demanding role. The pressures from Covid-19 only compounded this. They’re responsible for supporting a new hybrid working model and fending off the rapidly evolving information security risks, whilst under even closer watch from the industry and data protection regulators, and of course, the board.
“CISOs must demonstrate a higher level of effectiveness than ever before”.
Sam Olyaei, Research Director, Gartner Top Security and Risk Trends for 2021.
The Gartner research states that the most successful are those who are proactive, reacting to any given situation with agility and flexibility. The report suggests that to boost productivity and effectiveness, CISOs should ensure they are up-to-date on the very latest threat landscape, that this is communicated internally to stakeholders and that this insight drives formally planning.
Effective time management is crucial. Whilst it is a skill that CISOs are naturally very adept at, in today’s fast-paced businesses, it can prove to be harder than it sounds with the majority of tasks appearing to be of equal importance. So what else can CISOs do to help them maximise their time and their chances of success?
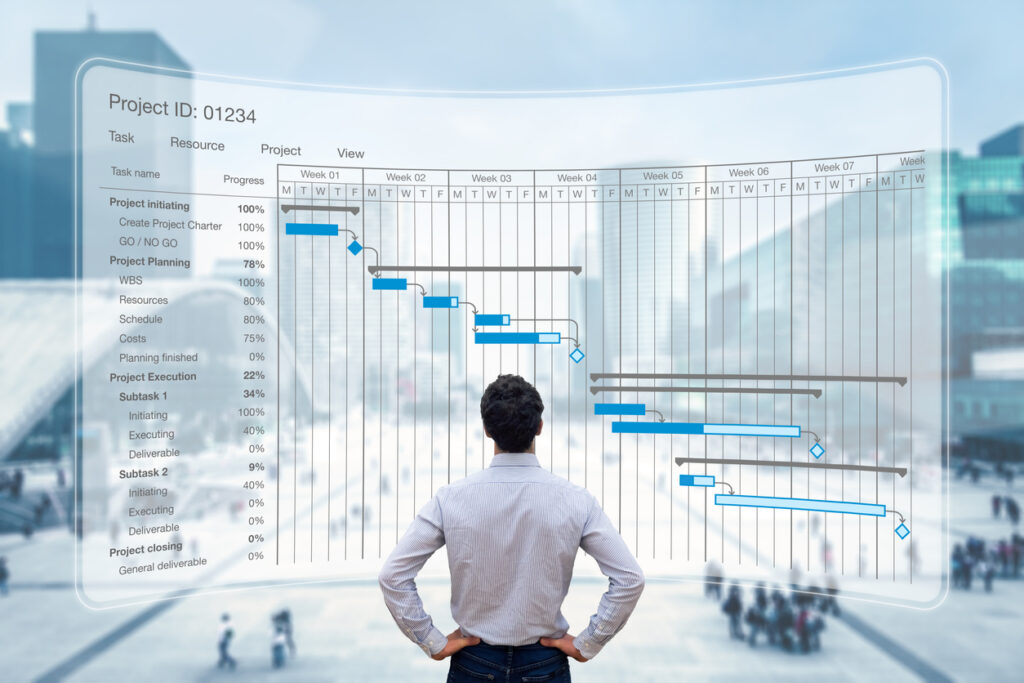
Follow project management best practice.
Whether are looking to undertake a secure office relocation or are embarking on full data centre decommissioning, no two projects are the same. Although time is tight, meticulous planning of each step can ensure essential business continuity and reduce potentially costly mistakes in the long run.
By incorporating the basics of business ‘goal-focused’ project management, you can ensure that everything goes according to plan, resulting in a successful project delivery – on time and on budget. Even if you’re well aware of the fundamentals of project management, hiring or outsourcing to a certified PRINCE2 Project Manager will create a detailed work structure to plan, monitor, control and adapt the project where necessary as it evolves. Recognised globally and highly effective for IT strategies, PRojects IN Controlled Environments (PRINCE2) is the world’s most practised project management method. It is scalable and will deliver time-saving methods that you may never have thought of.
A common consistent, controlled approach with assigned roles and controllable stages, this form of project management focuses on the goals, resources, and schedule but will also highlight the next steps that are required, such as on-site data erasure of end-of-life IT assets, for example.
Delegate IT asset management.
As any CISO will tell you, the most important resource they have available to them is a strong, skilful team. Nothing supports your effectiveness as a CISO more than reliable, capable direct reports. These are great time-enablers, allowing the delegation of day-to-day, time-zapping tasks, such as internal IT asset management.
If you already follow best practice and outsource ITAD, it is highly likely that your IT supplier provides lifecycle services alongside data erasure. By combining these services, you create a joined- up approach to asset management, data destruction services and free IT asset disposal.
IT preparation, roll-out, and installation services can relieve pressure on internal team members, so they can provide support for other projects. Purchasing, pre-installing software, PAT testing and imaging can be undertaken off-site to reduce the use of internal resources. On-site deployment and set-up can often be undertaken out of hours to prevent disruption to your team’s working day.
When redundant IT assets are marked for resale or recycling, data erasure services will issue each piece of equipment with its own IT asset disposal accreditation certificate; preventing any future data governance issues. IT asset disposal services are experts in data protection and waste management legislation and as the ITAD chain of custody is such a critical point for regulatory compliance, delegating will relieve a little added pressure.
64% of employees are now able to work from home. Two-fifths actually are.
Gartner CIO Survey 2021.
Remote working has evolved and is now just ‘work’ for many, but from an information security perspective, the changing practices have required new policies and the provision of upgraded machines to mitigate the risks. Although deployment and collection of assets to hundreds if not thousands of locations is a considerable administrative headache. Many IT asset disposal companies now offer circular solutions to support in-house teams and reduce management time when it comes to the roll-out of new IT infrastructure along with the collection and disposal of legacy equipment.

Undertake a full IT asset inventory.
If you have adopted a hybrid model or still have some employees that are yet to return to the office, it is essential that your hardware inventory is regularly monitored and updated – not doing so is one of the most common ITAD mistakes. It is easy to lose track. You may accidentally leave your data-rich IT assets with previous employees, unprotected from the corporate firewall, antivirus or anti-malware.
CISOs are pulled in multiple directions and given the pace we all now work at, it is essential that the appropriate documentation is created to eliminate risks to your data security. After the unplanned and rapid deployment of teams to home offices across the region, it would be a good idea to conduct an IT asset data audit, providing you with an up-to-date, complete inventory.
Asset tracking requires the custody of every single asset verified. Traditional tracking assets by matching serial numbers and asset tags to existing inventories is tedious, time-consuming and often unreliable. A multi-year study revealed only about half of serial numbers captured by ITAD vendors perfectly match against anticipated inventory. A far more effective method is to track assets using barcodes, much like airlines track luggage. Barcode asset tags increase tracking to 99% effectiveness, rather than 50%.
Not only is a full audit a good way to double-check that all is as it should be, it can help you to highlight any surplus equipment for redistribution or resale; freeing up the departmental budget.
With many offices still at half their capacity, older hardware is sitting gathering dust. Your ITAD partner could sanitise and prepare equipment for either storage, resale or redeployment. Equipment can be updated to a newer OS or erased and recycled securely to protect company data. Similarly, by auditing your technology, you can identify and cancel services that you no longer use or really need.
With the added pressures from an increasingly digital infrastructure, delegation can be an effective time management strategy for CISO’s. Although it still requires careful management, project management, IT asset auditing and lifecycle services can deliver a circular approach – maximising time, maximising efficiencies and minimising risks.
By maximising departmental effectiveness, CISOs can focus more on their top-line priorities, helping to mitigate the risks associated with a corporate data breach. Given the increased level of cybersecurity threats and the tighter EU and UK GDPR data destruction requirements, the importance of asset disposal should not be underestimated.
Acting as an extension of your team, we are here to help. Find out more about our timesaving support services, including IT asset audits, working from home and lifecycle services. tier1 can also assist with your secure office relocation, asset upgrades or recycling of redundant IT equipment.
To find out more, call us on 0161 777 1000 (Manchester), 01621 484380 (Maldon) or visit www.tier1.com/contactus
Resources.
CIO, CIO Insight, Gartner, Computer Weekly, Retire IT, Prince2, Microsoft,



